On January 22, 2026, Xiaomi launched the HyperOS 3.1 beta, which included minor but significant UI and privacy improvements. Phones become smoother and speedier as a result. Additionally, the HyperOS 3.1 update uses AI to extend battery life.
With improved app switching and adjustable settings, it improves the user interface. Additionally, it offers improved multitasking, smoother animations, and increased privacy and security.
A more reliable, refined, and connected experience is provided by HyperOS 3.1. It also offers support for iOS calls and security updates for Android 16. Let’s examine the characteristics of HyperOS 3.1 in more detail below:
Quick look at Xiaomi HyperOS 3.1 features coming to your device
| Category | Feature | Explanation |
| iOS Integration | AirPods Native Pop-Up | Let users hide unlock pattern traces |
| iOS Integration | Spatial Audio Support | Enables 360-degree immersive audio on Xiaomi phones |
| iOS Integration | ANC & Transparency Control | Manage noise cancellation and sound modes easily |
| iOS Integration | Find My AirPods | Locate lost AirPods without needing an Apple ID |
| UI & Animations | New System Animations | Smoother, more fluid transitions across the system |
| UI & Animations | iOS-Style Recent Apps | Card-like multitasking view inspired by iOS |
| Apps Overhaul | New Gallery & Weather Apps | Faster apps with rewritten code for better performance |
| Accessibility | New “Assistance” Menu | Easier access to vision, hearing, and control tools |
| Accessibility | Active Visual Perception | Helps users better understand on-screen content |
| Motion & Comfort | Motion Sickness Feature | Reduces visual motion to prevent dizziness |
| Super Island | Live Update Support | Real-time updates from apps like Uber and Spotify |
| Super Island | Todo Notes & QR Access | View tasks, QR codes, and maps directly on Island |
| Lock Screen | Card Swipe Support | Swipe payment and transit cards on lock screen |
| Media | Music Progress Bar | iOS-style glowing progress bar on media player |
| Ecosystem | Xiaomi + iPhone Call Support | Answer Xiaomi calls directly on an iPhone |
| System Core | Biometric Redesign | Improved fingerprint and unlock settings |
| System Core | Quick Gestures | Faster gesture shortcuts on select premium phones |
| Security | New Password App | Stores passwords, Wi-Fi logins, and passkeys |
| Security | Password Breach Alerts | Warns if your passwords are compromised |
| Privacy | Shake Permission Update | Limits app access to camera, mic, or location |
| Privacy | Hidden Pattern Trail | Lets users hide unlock pattern traces |
| Performance | Faster & Smoother System | Improved speed and stability |
| Battery | AI Battery Optimization | Smarter power saving using AI |
| Android Core | Android 16 Security Patches | Latest system-level security improvements |
iOS integration
You may have overlooked many Apple-only features if you have Apple AirPods and a Xiaomi phone. The AirPods’ battery level was visible before the introduction of Xiaomi HyperOS 3.1. Similar to Apple AirPods, Xiaomi phones have developed as a local brother that will never be alone.
Important improvements like Apple-like native Pop Up support are included in the latest version of HyperOS 3.1. A brief card with details about the battery and connectivity now appears on your screen when you open the AirPod
Spatial Auido, one of Apple’s most exclusive features, is now accessible. Users of Xiaoimi can now enjoy native 360-degree immersive audio. Additionally, the HyperOS club allows you to control the connection time, ANC, and Transparency mode.
Additionally, instead of displaying the standard Bluetooth icon, it only displays the appropriate AirPods model icon. Notably, Xiaomi’s “Find My” Integration allows you to locate your misplaced AirPods using Xiaomi Online Search without even requirin
New UI animations
Xiaomi rewrites Gallery and Weather and changes its animations. To enhance system performance, all outdated code has been eliminated. The new APK files will crash when installed on older HyperOS 3 devices as a result of this modification.

Additionally, the company imitated the latest iOS 26 app animation. Switching between programs feels more contemporary because to the new style, which resembles the iOS cards.
Improvements have been made to the white bar at the bottom of the screen that indicates when you are in full-screen mode. It now responds better to touch and moves more fluidly.
HyperOS 3.1 now has a new Motion Sickness function from Xiaomi. Motion sickness-causing visual motion cues are lessened by this featur
Improved Super Island
Although Super Island now uses the native Android 16 “Live update” API, it was completely inspired by iOS Dynamic Island. Thus, Xiaomi-specific code will no longer be required for international apps such as Uber, Spotify, or other food delivery services to display real-time information on Super Island
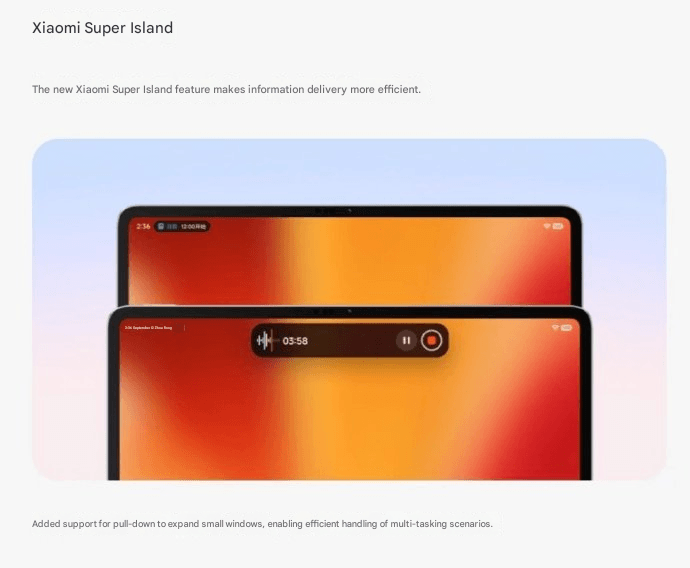
Following this upgrade, Xiaomi added a Todo Notes feature. You no longer need to open the app landing page in order to view a variety of notifications, QR codes, and map instructions in Island. Additionally, a function known as Lock Screen Card Swipe is added. This makes it simple to swipe through your cards, including transit and payment cards, directly on the lock screen. You won’t have to visit a different wallet website.
The new Music Progress Bar, which was completely lifted from iOS, is one of my favorites. The media player on the island now has a glowing progress bar thanks to a straightforward yet lovely modification.
System Core enhancements
The “Assistance” Menu functionality was implemented in HyperOS 3.1 (Accessibility Settings Change). This indicates that Xiaomi renamed and relocated the accessibility options to a new main menu called “Assistance.” Those who require simpler phone controls or who have vision or hearing issues can benefit from these options.
Features, for instance, relocated there. Active Visual Perception improves the clarity of what users see or comprehend on the screen. Screen readers, text size control, and tools for hearing and vision assistance.
Additionally, the new biometric area offers a more contemplative experience. Additionally, Xiaomi included Quick Gestures control, which is only available on more recent high-end models like the Poco F8 Ultra and Redmi K90 Pro Max.
As I have stated, deep ecosystems are greatly impacted by Apple AirPod integration. Additionally, the most crucial brick is iPhone Cross-Compatibility (Xiaomi + iPhone). You can now answer and receive calls from your Xiaomi phone directly on your iPhone if you have both an iPhone and a Xiaomi phone. To put it simply:
When your Xiaomi phone calls, you may answer it on your iPhone. Thus, you don’t always need to touch your Xiaomi phone. Since Apple and Xiaomi often don’t collaborate closely, this function is unique in that it links two competing ecosystems.
Many security improvements

The Passwprd App, similar to iOS, is now one of the key features of HyperOS 3.1. Similar to Apple, this new tool helps you manage your Wi-Fi passwords, passkeys, and app logins.
It can detect and alert you if your passwords have been stolen. Additionally, it allows you to manage all of your passwords in one location by combining them from several online browsers. Additionally, it offers a simple method for your passwords to be automatically filled in throughout the system.
The way you can use patterns and fingerprints has changed in the latest release. The pattern trace can now be concealed once more. Additionally, it is now simpler to select your security options because the fingerprint unlock is independent of the private password settings.
Shake Permission Update is a new function that allows you to modify your privacy. This enables you to restrict access to your location and camera, for example, only when your screen is on. Additionally, you have the option to restrict these permissions to eight seconds following the opening of an application. By doing this, you can stop apps from following you when you’re not

Overall, HyperOS 3.1’s improvements prioritize polish over a significant redesign, enhancing ecosystem connectivity, privacy, battery efficiency, and smoothness. This beta seems more polished, reliable, and prepared for the future than earlier HyperOS iterations thanks to Apple-inspired features and Android 16 security improvements.